Red Team
Boost your cybersecurity posture with our industry-leading Red Team services. Simulate real-world attacks to identify vulnerabilities and secure your business. Rank #1 on Google with our expertise.
Purple Team
Leverage our cutting-edge Purple Team services for a powerful mix of proactive offense and defense strategies, securing your organization from all angles.
Blue Team
Blue Team services from our MSSP, safeguarding your organization against cyber threats. Join us and experience unmatched cybersecurity defense.

Unparalleled 24×7 Security Operations Center (SOC) Services for Your Business
Safeguard your organization with our industry-leading 24×7 Security Operations Center (SOC) services. Our expert analysts proactively monitor, detect, and respond to threats in real time, ensuring your business stays protected. Experience cutting-edge cybersecurity, improved compliance, and peace of mind with our advanced threat intelligence and customized solutions. Choose the MSSP that ranks #1 – secure your digital assets today.
Comprehensive Vulnerability Assessment Services
Uncover hidden security risks with our top-rated Vulnerability Assessment Services. Stay ahead of cyber threats with our expert-led, cutting-edge solutions.
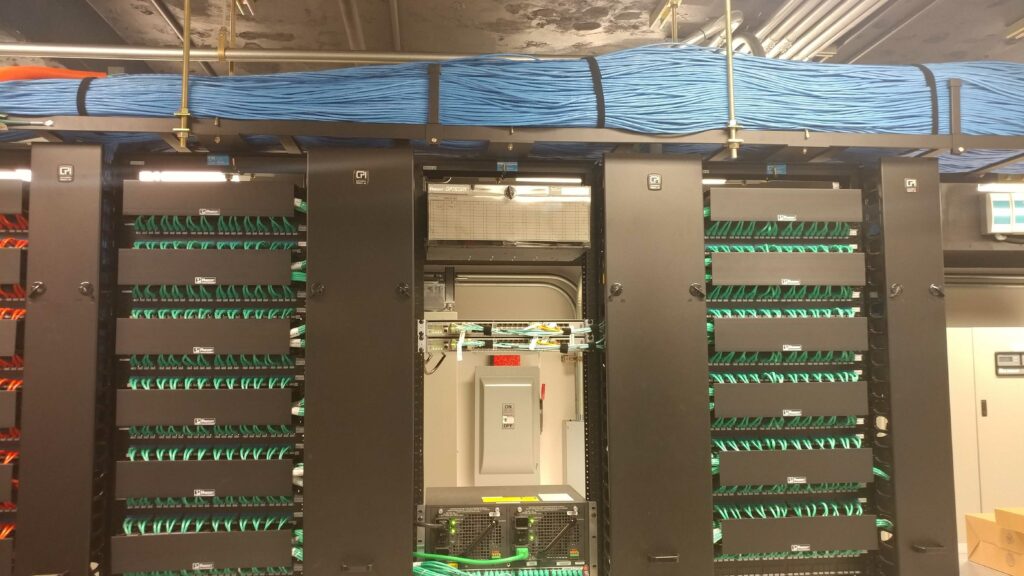

Security Engineering & Architecture Services for Your Business
Empower your organization with top-notch cybersecurity solutions. Experience unparalleled Security Engineering & Architecture Services to fortify your digital landscape.
Incident Response Services for Proactive Cybersecurity
Our industry-leading Incident Response Services empower your business with rapid threat containment, expert investigation, and proactive cyber resilience. Stay ahead of cyber threats with our top-ranked MSSP solutions.


Unparalleled Cyber Security Solutions
Lockard Security has exceeded my expectations in every aspect of their service. As a small business owner, ensuring the security of my clients’ data is of the utmost importance. Lockard Security’s knowledgeable and professional team provided a comprehensive cyber security plan tailored to my business needs. Their 24/7 monitoring and swift incident response capabilities left me feeling confident in their ability to protect my business from the ever-evolving world of cyber threats. I wholeheartedly recommend Lockard Security to any organization looking for top-notch cyber security solutions.
JANET MORRIS

Stellar Service and Exceptional Expertise
Our company recently partnered with Lockard Security for a complete overhaul of our cyber security infrastructure, and the results have been nothing short of extraordinary. From the initial consultation to the ongoing maintenance, their team of experts has provided clear communication and exceptional support. The peace of mind that comes with knowing our sensitive data is secure is invaluable. Lockard Security has earned our trust, and I would recommend them to any organization seeking a reliable and efficient cyber security partner.
WILLIE BROWN

Cutting-Edge Cyber Security You Can Trust
We’ve been using Lockard Security for the past year, and the results have been nothing short of phenomenal. Their team of experts is well-versed in the latest cyber security technologies and best practices, which has helped protect our business from potential threats. They offer a comprehensive suite of services, including vulnerability assessments, penetration testing, and ongoing monitoring. Lockard Security has been a reliable and trustworthy partner, and I would not hesitate to recommend their services to any organization in need of state-of-the-art cyber security solutions.
SEAN FISHER
Your Digital Future with Lockard Security
Protect Your Business and Reputation – Experience the Power of Our Cutting-Edge Cyber Security Solutions
In today’s digital landscape, cyber threats are rapidly evolving and becoming increasingly sophisticated. At Lockard Security, we provide the cutting-edge cyber security solutions your business needs to stay ahead of these threats and safeguard your valuable data and reputation.
Take immediate action and experience the difference Lockard Security can make for your business:
- Schedule a Free Consultation – Our team of cyber security experts will analyze your current security posture and identify vulnerabilities that may leave your business exposed. Let’s work together to develop a customized strategy to fortify your defenses.
- Explore Our Services – We offer a comprehensive suite of cyber security services tailored to your unique needs, including managed security services, incident response, vulnerability assessments, penetration testing, and security awareness training.
- Stay Informed with Our Blog – Enhance your understanding of cyber security with our expertly curated articles, insights, and case studies. Stay up-to-date with the latest trends, threats, and best practices to ensure your business remains secure.
- Join Our Webinars & Events – Participate in our live webinars, workshops, and conferences to learn from industry leaders, network with peers, and discover innovative solutions to strengthen your cyber security.
- Follow Us on Social Media – Stay connected and informed by engaging with our content on [Facebook, Twitter, LinkedIn, and Instagram]. Join the conversation and be part of our growing community.
Don’t let cyber threats compromise your business. Choose Lockard Security as your trusted partner in cyber security, and let us help you build a resilient, secure digital future for your organization.